Sql-Injection-Proof-of-Concept: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
| Zeile 1: | Zeile 1: | ||
| + | =Test Seite= | ||
| + | *https://sql.willux.de/ | ||
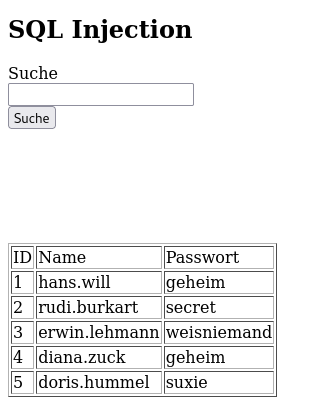
| + | =Unsichere Seite= | ||
| + | [[Datei:sql-injection-1.png]] | ||
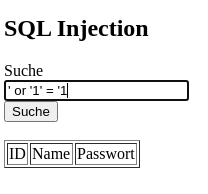
| + | =Sichere Seite= | ||
| + | [[Datei:sql-injection-2.png]] | ||
| + | |||
| + | |||
| + | |||
=Unsichere Methode= | =Unsichere Methode= | ||
<pre> | <pre> | ||
Version vom 7. Oktober 2020, 16:49 Uhr
Test Seite
Unsichere Seite
Sichere Seite
Unsichere Methode
<?php
if(isset($_POST['submit'])){
//connect db
include "inc/connect.php";
//unsafe query
$search = $_POST['search'];
//Database search
$sql = "SELECT * FROM users WHERE username='$search'";
$result = mysqli_query($link, $sql);
}
?>
<!DOCTYPE html>
<html>
<body>
<h2>SQL Injection</h2>
<form method="post">
<label for="fname">Suche</label><br>
<input type="text" name="search"><br>
<input type="submit" name="submit" value="Suche">
</form>
<br>
<table border = "1">
<tr>
<td>ID</td>
<td>Name</td>
<td>Passwort</td>
</tr>
<?php
while ($row = mysqli_fetch_row($result)) {
echo "<tr>";
echo "<td>".$row[0]." </td>";
echo "<td>".$row[1]." </td>";
echo "<td>".$row[2]." </td><br>";
echo "</tr>";
}
?>
</table>
</body>
</html>
Sichere Methode
<?php
if(isset($_POST['submit'])){
//connect db
include "inc/connect.php";
//safe query
$search = mysqli_real_escape_string($link, $_POST['search']);
//Database search
$sql = "SELECT * FROM users WHERE username='$search'";
$result = mysqli_query($link, $sql);
}
?>
<!DOCTYPE html>
<html>
<body>
<h2>SQL Injection</h2>
<form method="post">
<label for="fname">Suche</label><br>
<input type="text" name="search"><br>
<input type="submit" name="submit" value="Suche">
</form>
<br>
<table border = "1">
<tr>
<td>ID</td>
<td>Name</td>
<td>Passwort</td>
</tr>
<?php
while ($row = mysqli_fetch_row($result)) {
echo "<tr>";
echo "<td>".$row[0]." </td>";
echo "<td>".$row[1]." </td>";
echo "<td>".$row[2]." </td><br>";
echo "</tr>";
}
?>
</table>
</body>
</html>