Strongswan zu strongswan psk ikev2 site to site: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
| (20 dazwischenliegende Versionen desselben Benutzers werden nicht angezeigt) | |||
| Zeile 1: | Zeile 1: | ||
| − | |||
==ipsec.conf== | ==ipsec.conf== | ||
===Erklärung=== | ===Erklärung=== | ||
*/etc/[[ipsec.conf Erklärung]] | */etc/[[ipsec.conf Erklärung]] | ||
===Datei=== | ===Datei=== | ||
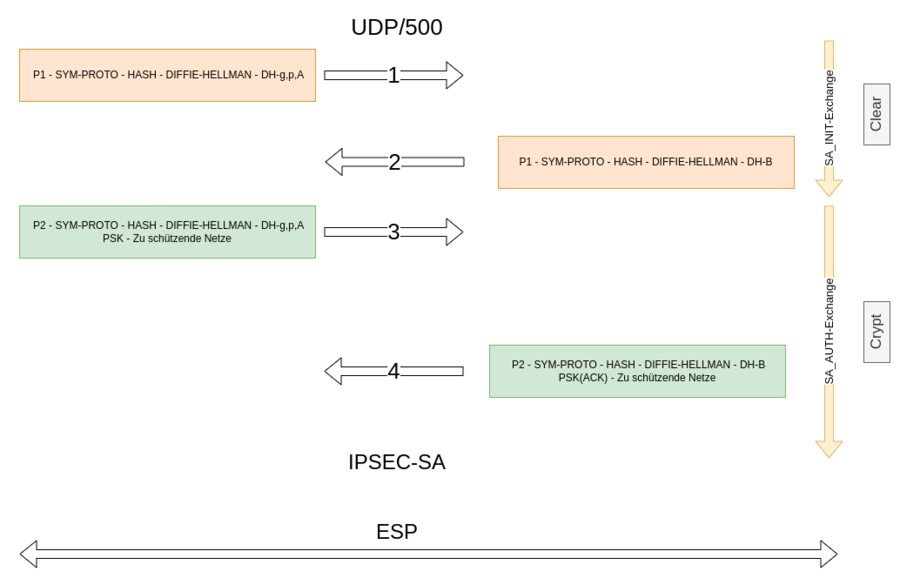
| + | [[Datei:Ikev2-prinzip.png|900px]] | ||
<pre> | <pre> | ||
conn s2s | conn s2s | ||
authby=secret | authby=secret | ||
keyexchange=ikev2 | keyexchange=ikev2 | ||
| − | left=10. | + | left=10.81.1.10 |
| − | leftsubnet= | + | leftsubnet=192.168.10.0/24 |
mobike=no | mobike=no | ||
| − | right=10. | + | right=10.81.1.11 |
| − | rightsubnet= | + | rightsubnet=192.168.11.0/24 |
ike=aes256-sha256-modp4096! | ike=aes256-sha256-modp4096! | ||
esp=aes256-sha256-modp4096! | esp=aes256-sha256-modp4096! | ||
| Zeile 23: | Zeile 23: | ||
;ID Kombination mit Authentifizierungsmethodes | ;ID Kombination mit Authentifizierungsmethodes | ||
*cat /etc/ipsec.secrets | *cat /etc/ipsec.secrets | ||
| − | 10. | + | 10.81.1.10 10.81.1.11 : PSK "suxer" |
=Handling= | =Handling= | ||
=Up= | =Up= | ||
*ipsec up s2s | *ipsec up s2s | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=Down= | =Down= | ||
*ipsec down s2s | *ipsec down s2s | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=Status= | =Status= | ||
| Zeile 71: | Zeile 39: | ||
s2s{4}: 10.82.243.0/24 === 10.82.244.0/24 | s2s{4}: 10.82.243.0/24 === 10.82.244.0/24 | ||
=TCPDump der Verbindung= | =TCPDump der Verbindung= | ||
| − | *tcpdump -ni eth0 port 500 or esp | + | *tcpdump -ni eth0 port 500 or esp |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=Mehrere Subnetze= | =Mehrere Subnetze= | ||
| Zeile 96: | Zeile 48: | ||
authby=secret | authby=secret | ||
keyexchange=ikev2 | keyexchange=ikev2 | ||
| − | left=10. | + | left=10.81.1.10 |
| − | + | leftsubnet=192.168.10.0/24 | |
| − | leftsubnet= | ||
mobike=no | mobike=no | ||
| − | right=10. | + | right=10.81.1.11 |
| − | + | rightsubnet=192.168.11.0/24,192.168.33.0/24 | |
| − | |||
ike=aes256-sha256-modp4096! | ike=aes256-sha256-modp4096! | ||
esp=aes256-sha256-modp4096! | esp=aes256-sha256-modp4096! | ||
| Zeile 108: | Zeile 58: | ||
</pre> | </pre> | ||
*ipsec status | *ipsec status | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=Links= | =Links= | ||
*https://www.heise.de/security/artikel/Einfacher-VPN-Tunnelbau-dank-IKEv2-270056.html | *https://www.heise.de/security/artikel/Einfacher-VPN-Tunnelbau-dank-IKEv2-270056.html | ||
Aktuelle Version vom 10. September 2023, 11:37 Uhr
ipsec.conf
Erklärung
- /etc/ipsec.conf Erklärung
Datei
conn s2s
authby=secret
keyexchange=ikev2
left=10.81.1.10
leftsubnet=192.168.10.0/24
mobike=no
right=10.81.1.11
rightsubnet=192.168.11.0/24
ike=aes256-sha256-modp4096!
esp=aes256-sha256-modp4096!
auto=start
ipsec.secrets
- ID Kombination mit Authentifizierungsmethodes
- cat /etc/ipsec.secrets
10.81.1.10 10.81.1.11 : PSK "suxer"
Handling
Up
- ipsec up s2s
Down
- ipsec down s2s
Status
- ipsec status s2s
Security Associations (1 up, 0 connecting):
s2s[4]: ESTABLISHED 7 seconds ago, 10.82.227.12[10.82.227.12]...10.82.227.22[10.82.227.22]
s2s{4}: INSTALLED, TUNNEL, reqid 1, ESP SPIs: cef198fc_i c4de821a_o
s2s{4}: 10.82.243.0/24 === 10.82.244.0/24
TCPDump der Verbindung
- tcpdump -ni eth0 port 500 or esp
Mehrere Subnetze
alice und tiazel
- /etc/ipsec.conf
conn s2s
authby=secret
keyexchange=ikev2
left=10.81.1.10
leftsubnet=192.168.10.0/24
mobike=no
right=10.81.1.11
rightsubnet=192.168.11.0/24,192.168.33.0/24
ike=aes256-sha256-modp4096!
esp=aes256-sha256-modp4096!
auto=start
- ipsec status