OPNsense site2site IPSEC: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
| Zeile 2: | Zeile 2: | ||
==Kenndaten== | ==Kenndaten== | ||
{| class="wikitable" | {| class="wikitable" | ||
| − | ! Einstellung !! opnsense. | + | ! Einstellung !! opnsense.it213.xinmen.de !! opnsense.it214.xinmen.de |
|- | |- | ||
| '''Protokoll 2''' || colspan="2" | IKEv2 | | '''Protokoll 2''' || colspan="2" | IKEv2 | ||
|- | |- | ||
| − | | '''IP Address''' || 192.168.hs. | + | | '''IP Address''' || 192.168.hs.213 || 192.168.hs.214 |
|- | |- | ||
| − | | '''Internes Netz''' || 172.17. | + | | '''Internes Netz''' || 172.17.213.0/24 || 172.17.214.0/24 |
|- | |- | ||
| '''Pre-Shared Key (PSK)''' || colspan="2" | 123Start$ | | '''Pre-Shared Key (PSK)''' || colspan="2" | 123Start$ | ||
| Zeile 20: | Zeile 20: | ||
| '''ESP-LIFETIME''' || colspan="2" | 3600s | | '''ESP-LIFETIME''' || colspan="2" | 3600s | ||
|} | |} | ||
| − | |||
==Beide Seiten== | ==Beide Seiten== | ||
Version vom 18. Februar 2026, 06:07 Uhr
VPN Daten
Kenndaten
| Einstellung | opnsense.it213.xinmen.de | opnsense.it214.xinmen.de |
|---|---|---|
| Protokoll 2 | IKEv2 | |
| IP Address | 192.168.hs.213 | 192.168.hs.214 |
| Internes Netz | 172.17.213.0/24 | 172.17.214.0/24 |
| Pre-Shared Key (PSK) | 123Start$ | |
| Phase 1 | AES256 – SHA256 – DH16 | |
| Phase 2 | AES256 – SHA256 – DH16 | |
| IKE-LIFETIME | 10800s | |
| ESP-LIFETIME | 3600s | |
Beide Seiten
- Cipher Suits
- PROTO: IKEv2
- IKE: aes256-sha256-modp4096
- ESP: aes256-sha256-modp4096
- PSK: 123Start$
- IKE-LIFETIME: 3h
- ESP-LIFETIME: 1h
Links
- ID: 192.168.12.26
- VPNGW: 192.168.12.26
- NETZ: 172.26.20.0/22
- Firewall
- UDP 192.168.12.34 -> 192.168.12.26:500 - WAN - ALLOW
- ESP 192.168.12.34 -> 192.168.12.26 - WAN - ALLOW
- ANY 172.26.52.0/22 -> 172.26.20.0/22 IPSEC ALLOW
Rechts
- ID: 192.168.12.34
- VPNGW: 192.168.12.34
- NETZ: 172.26.52.0/22
- Firewall
- UDP 192.168.12.20 -> 192.168.12.34:500 - WAN - ALLOW
- ESP 192.168.12.26 -> 192.168.12.34 - WAN - ALLOW
- ANY 172.26.20.0/22 -> 172.26.52.0/22 IPSEC ALLOW
Schaubild
Firewall
- Wir gehen davon aus, das ausgehender Verkehr freigeschaltet ist.
- Die Gegenseite muss zu unserer Firewall UDP Port 500 und ESP Verbindungen aufbauen können.
- Desweiteren müssen die Partnernetze zu unseren Netzen freigeschaltet werden.
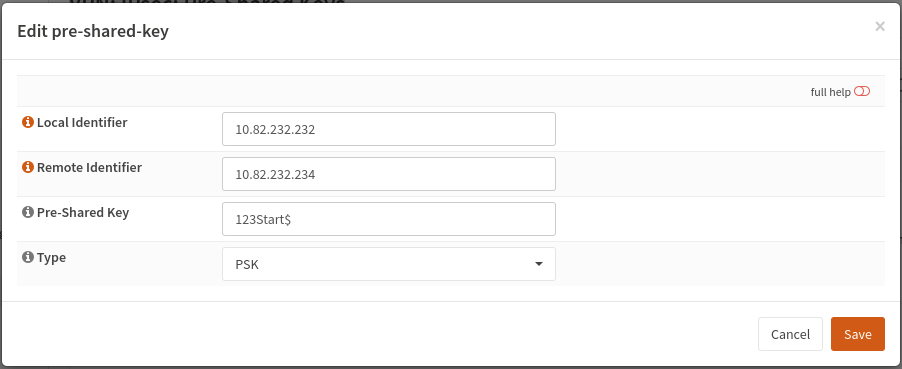
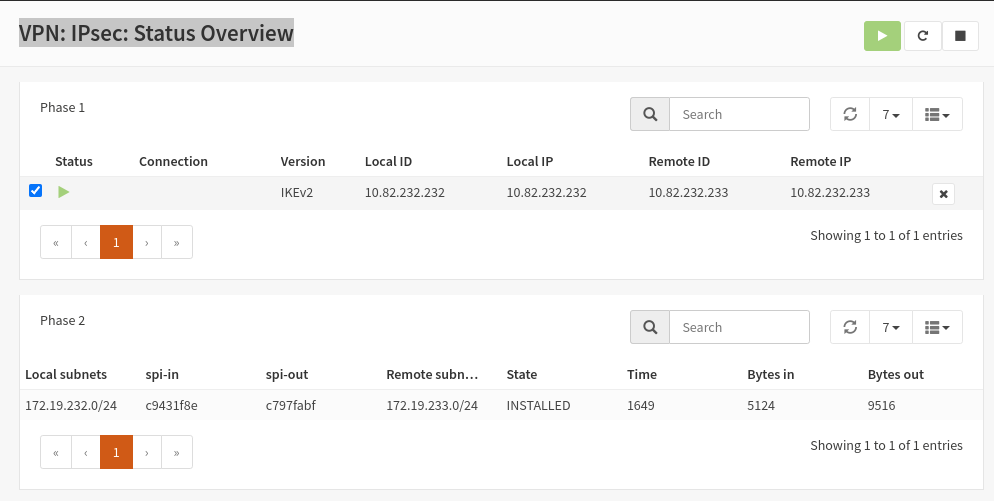
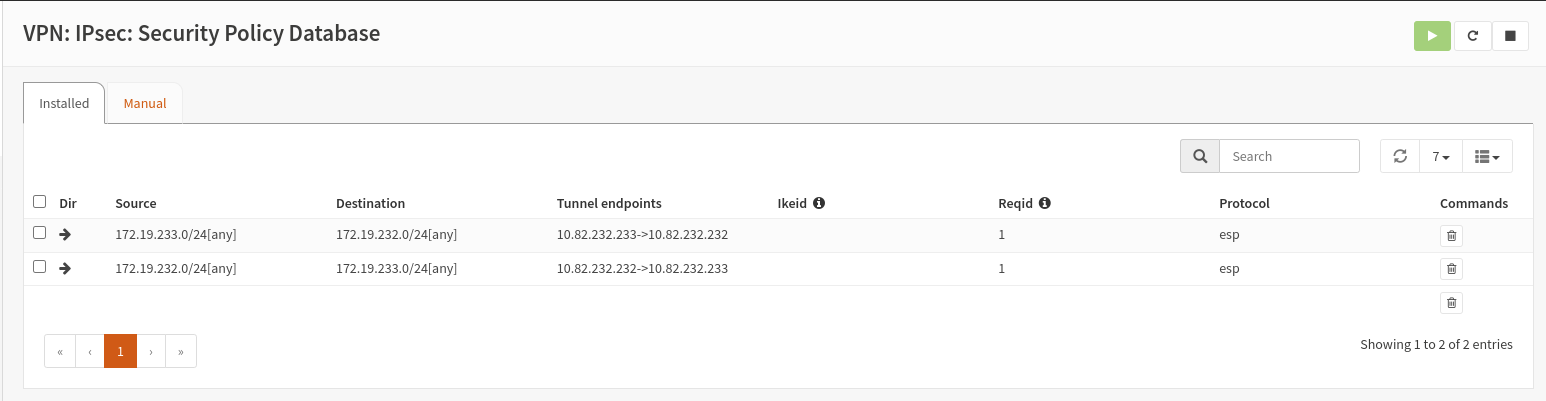
- VPN
- IPsec
- Pre-Shared Keys
- IPsec
VPN: IPsec: Connections
ADD PSK
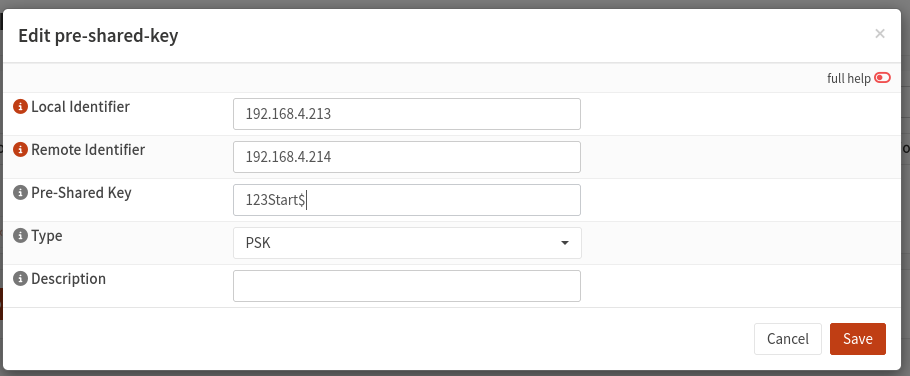
- VPN
- IPsec
- PREshared_Key
- IPsec
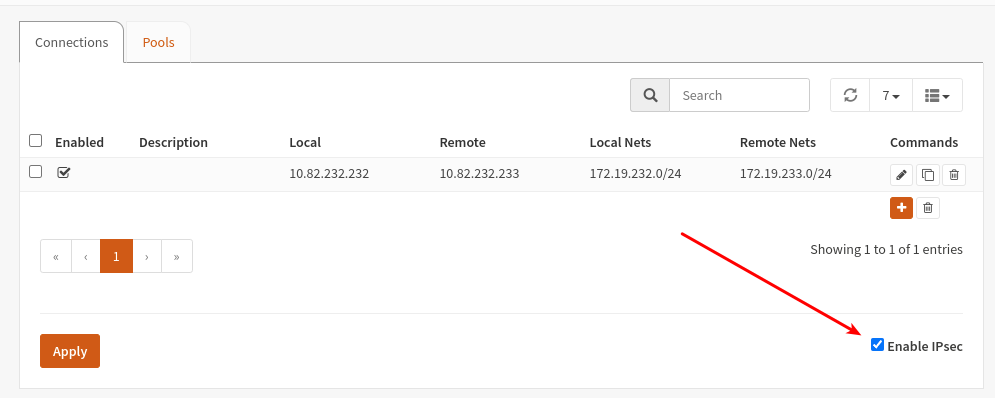
Enable IPsec
- VPN
- IPsec
- Connections
- IPsec
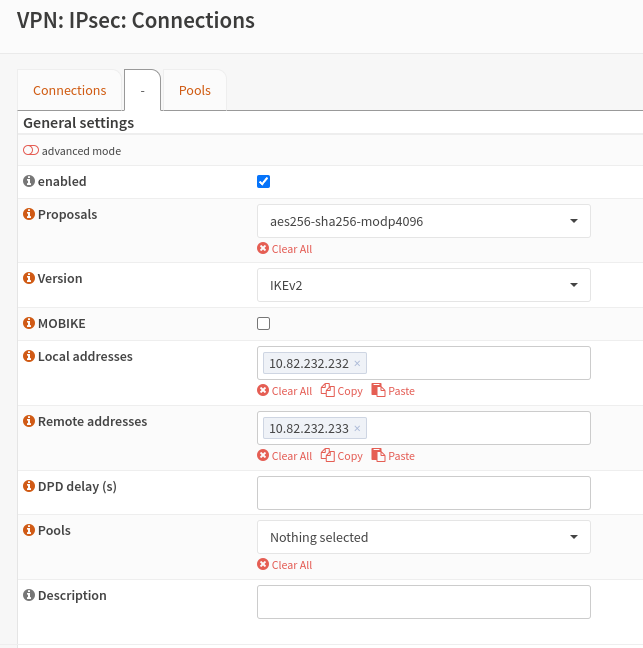
Add Connection
- VPN
- IPsec
- Connections
- IPsec
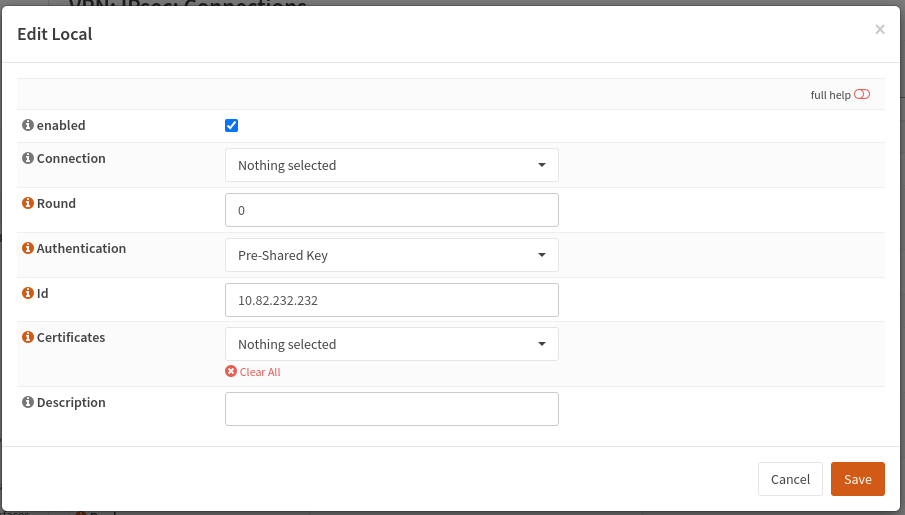
Local Authentication
- VPN
- IPsec
- Connections
- Local Authentication
- Connections
- IPsec
Remote Authentication
- VPN
- IPsec
- Connections
- Remote Authentication
- Connections
- IPsec
Children
- VPN
- IPsec
- Connections
- Children
- Connections
- IPsec