OPNsense Wireguard: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
| Zeile 1: | Zeile 1: | ||
=Konfiguration= | =Konfiguration= | ||
| − | * | + | *VPN |
| − | + | **WireGuard | |
| − | + | ***Settings => General''' | |
| − | + | {| class="wikitable" | |
| + | ! Bereich !! Einstellung !! Wert | ||
| + | |- | ||
| + | | VPN → WireGuard → Settings || Enable WireGuard || aktiviert | ||
| + | |- | ||
| + | | VPN → WireGuard → Settings || Status || Enabled | ||
| + | |- | ||
| + | | VPN → WireGuard → Settings || Aktion || Apply | ||
| + | |} | ||
| + | == WireGuard Instance – WG == | ||
| + | *VPN | ||
| + | **WireGuard | ||
| + | ***Settings | ||
| + | ****Instances | ||
| + | *****+ | ||
| + | {| class="wikitable" | ||
| + | ! Parameter !! Wert | ||
| + | |- | ||
| + | | Enabled || Ja | ||
| + | |- | ||
| + | | Name || WG | ||
| + | |- | ||
| + | | Instance || 0 | ||
| + | |- | ||
| + | | Public key || DaPF7JvnRYpNuXiFgo4Uqu/Yq9dmz0Gu8mijd4h... | ||
| + | |- | ||
| + | | Private key || gDvRj18foAvOVGTvZR6ca2ewRQBstGlg/I5cdPUA... | ||
| + | |- | ||
| + | | Listen port || 55555 | ||
| + | |- | ||
| + | | Tunnel address || 172.30.32.1/24 | ||
| + | |- | ||
| + | | Depend on (CARP) || None | ||
| + | |- | ||
| + | | Peers || client1, client2 | ||
| + | |- | ||
| + | | Disable routes || Nein | ||
| + | |- | ||
| + | | Debug log || Nein | ||
| + | |} | ||
| + | |||
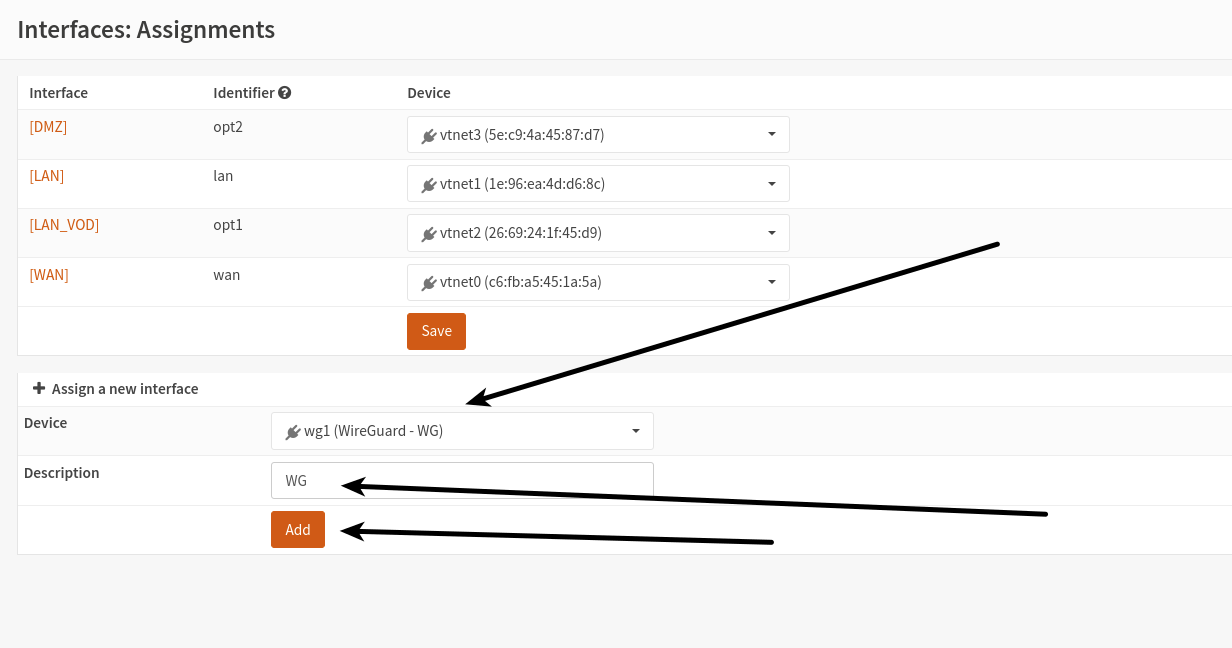
=Interfaces= | =Interfaces= | ||
*Assignments | *Assignments | ||
Version vom 18. Februar 2026, 13:17 Uhr
Konfiguration
- VPN
- WireGuard
- Settings => General
- WireGuard
| Bereich | Einstellung | Wert |
|---|---|---|
| VPN → WireGuard → Settings | Enable WireGuard | aktiviert |
| VPN → WireGuard → Settings | Status | Enabled |
| VPN → WireGuard → Settings | Aktion | Apply |
WireGuard Instance – WG
- VPN
- WireGuard
- Settings
- Instances
- +
- Instances
- Settings
- WireGuard
| Parameter | Wert |
|---|---|
| Enabled | Ja |
| Name | WG |
| Instance | 0 |
| Public key | DaPF7JvnRYpNuXiFgo4Uqu/Yq9dmz0Gu8mijd4h... |
| Private key | gDvRj18foAvOVGTvZR6ca2ewRQBstGlg/I5cdPUA... |
| Listen port | 55555 |
| Tunnel address | 172.30.32.1/24 |
| Depend on (CARP) | None |
| Peers | client1, client2 |
| Disable routes | Nein |
| Debug log | Nein |
Interfaces
- Assignments
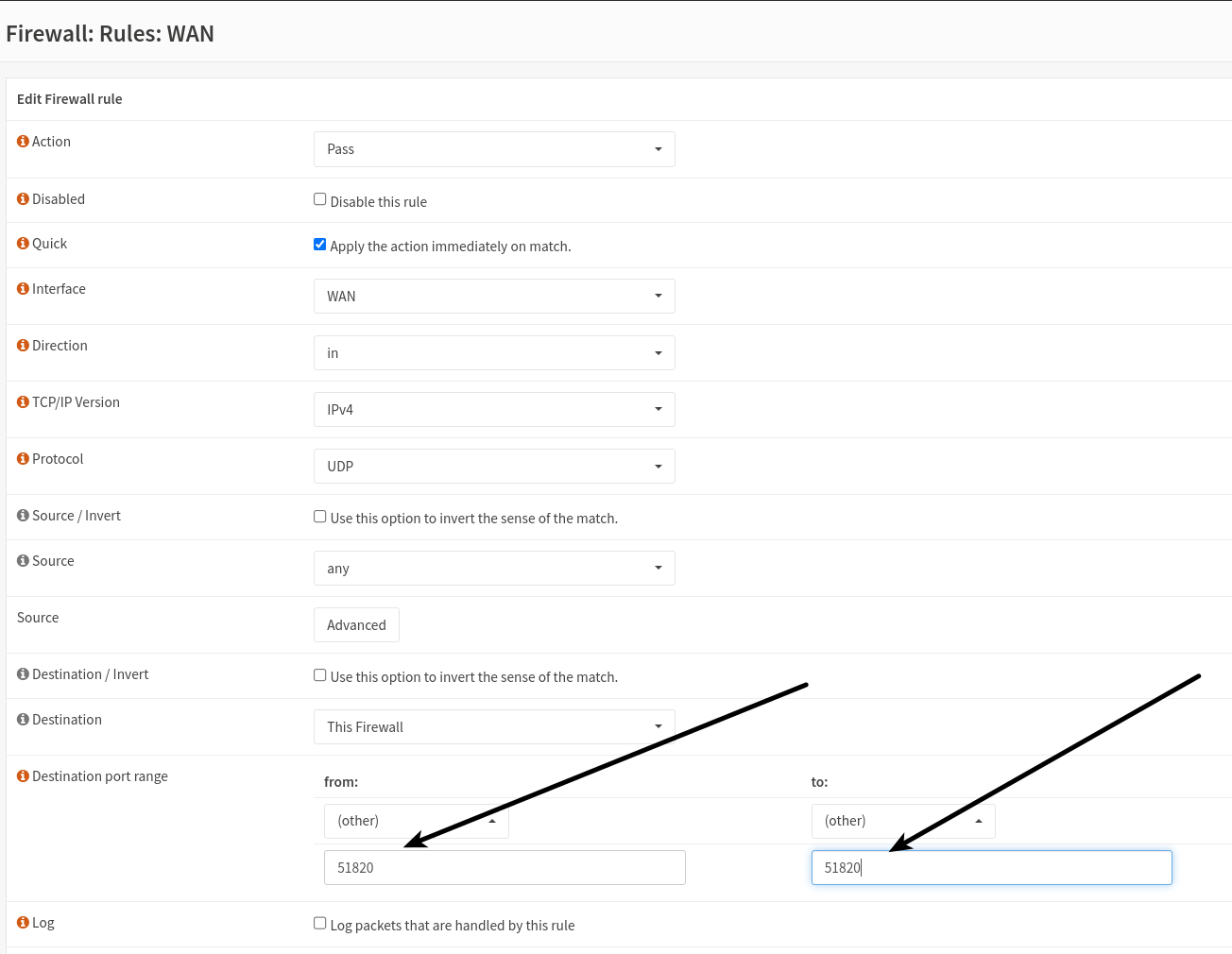
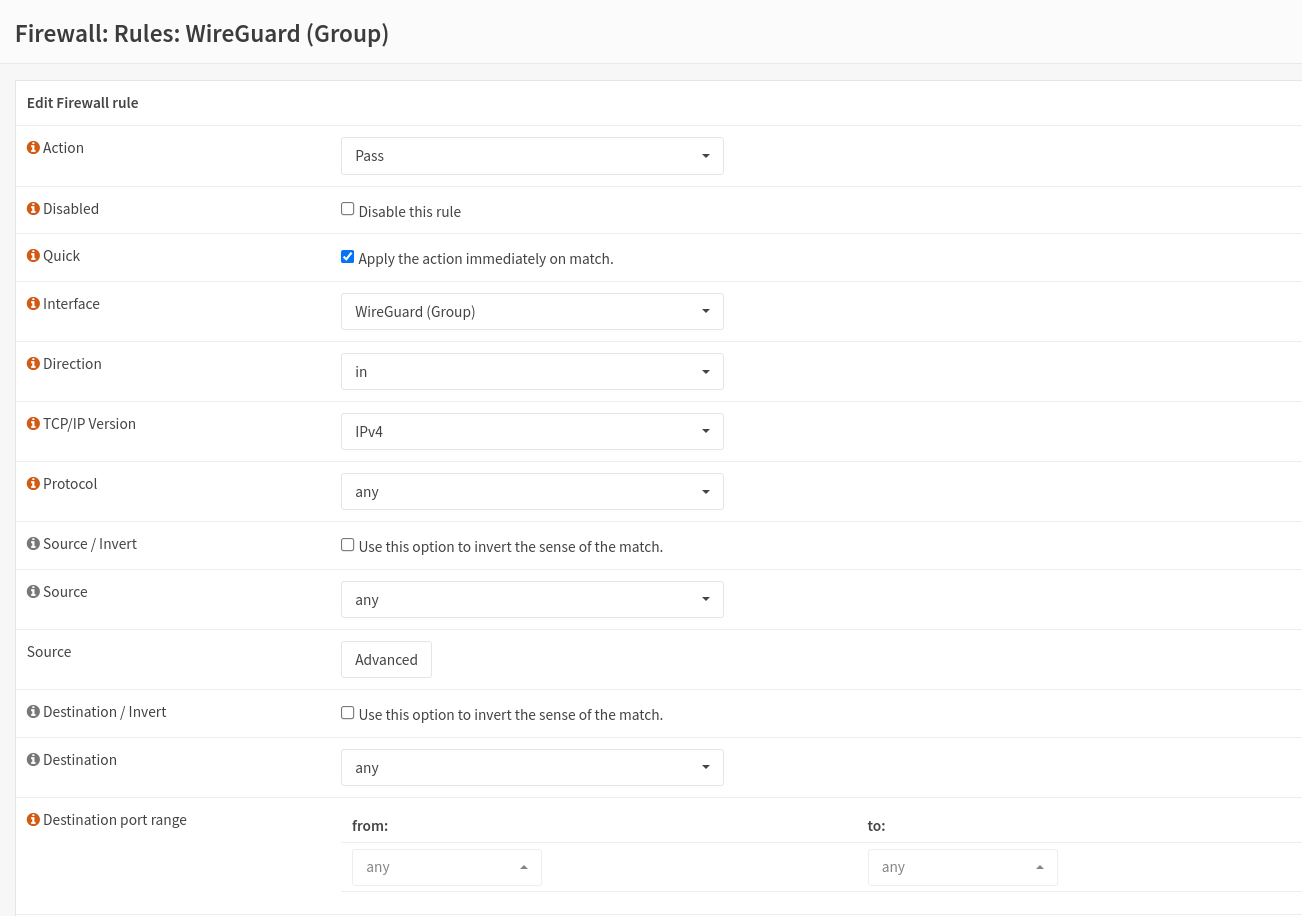
Firewall
- => Rules => WAN => +
- => Rules => WireGuard (Group) => +
An einem Linux System
- PUBKEY_SERVER=XbO5anN/a6S6fR40N6xn+lqkctdAZK4yudaVAUtVmh8=
- PRIVKEY=$(wg genkey)
- PUBKEY=$(echo $PRIVKEY | wg pubkey)
- cat<<HERE > client1.conf
[Interface] Address = 172.30.32.101/24 PrivateKey = $PRIVKEY #PUBKEY = $PUBKEY DNS = 8.8.8.8 [Peer] PublicKey = $PUBKEY_SERVER AllowedIPs = 0.0.0.0/0 Endpoint = opns-zw.ix.de:55555 HERE
generate the qrcode
- qrencode -t utf8 < client1.conf
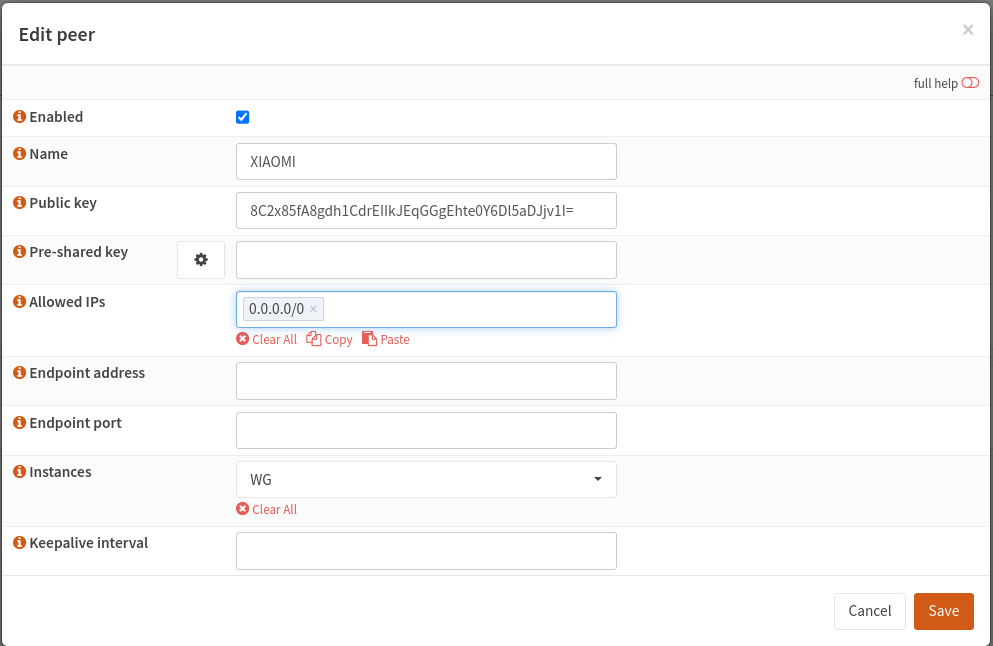
Peer hinzufügen
Auf Linux System
- Wireguard installieren
- sudo apt install wireguard
- Konfigurationsdatei der Opnsense einfügen
- sudo vi /etc/wireguard/wg0.conf
[Interface] PrivateKey = uNBjRjmVjfut59L8cAMxRGhcPdXi/BxtidSrDU+EWXU= Address = 172.30.32.2/32 [Peer] PublicKey = DaPF7JvnRYpNuXiFgo4Uqu/Yq9dmz0Gu8mijd4h622E= PresharedKey = 8/sxyen2B/1PeNsSe+KfgNuUJgF5F0y2RWcHZMtbXEU= Endpoint = opnsense.it213.xinmen.de:55555 AllowedIPs = 0.0.0.0/0,::/0 PersistentKeepalive = 10
Wireguard start
- sudo wg-quick up wg0
Wireguard stop
- sudo wg-quick down wg0
Wireguard show
- sudo wg show