Linux - Netzwerk und Serveradminstration Firewall: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
(Die Seite wurde neu angelegt: „= Firewall = {{#drawio:5102-firewall-01}} * Die Firewall wird ist zugleich der Router in das Übungsnetzwerk * Hardwareanpassungen: ** 4 GB RAM ** 4 CPUs ** 4…“) |
|||
| Zeile 1: | Zeile 1: | ||
| + | =Wir klonen das debian-template= | ||
| + | Folgendes stellen wir ein | ||
| + | ** Name fw | ||
| + | ** 4 GB RAM | ||
| + | ** 4 CPUs | ||
| + | ** 1. NIC WAN | ||
| + | ** 2. NIC LAN | ||
| + | ** 3. NIC LAN | ||
| + | ** 4. NIC SERVERS | ||
| + | |||
| + | |||
| + | |||
| + | |||
| + | |||
| + | =Erklärung= | ||
| + | *XX = Platznummer | ||
| + | *Y = Klassensaal | ||
| + | =Hostname= | ||
| + | *hostnamectl set-hostname fw.it2XX.int | ||
| + | |||
| + | =Interfaces= | ||
| + | *cat /etc/network/interfaces | ||
| + | <pre> | ||
| + | source /etc/network/interfaces.d/* | ||
| + | |||
| + | # The loopback network interface | ||
| + | auto lo | ||
| + | iface lo inet loopback | ||
| + | |||
| + | # The primary network interface | ||
| + | #WAN | ||
| + | auto enp0s3 | ||
| + | iface enp0s3 inet static | ||
| + | address 192.168.Y.2XX/24 | ||
| + | gateway 192.168.Y.254 | ||
| + | post-up ip route add 10.88.0.0/16 via 192.168.Y.88 | ||
| + | |||
| + | |||
| + | #LAN | ||
| + | auto enp0s8 | ||
| + | iface enp0s8 inet static | ||
| + | address 172.16.2XX.1/24 | ||
| + | |||
| + | #DMZ | ||
| + | auto enp0s9 | ||
| + | iface enp0s9 inet static | ||
| + | address 10.88.2XX.1/24 | ||
| + | |||
| + | #SERVERS | ||
| + | auto enp0s10 | ||
| + | iface enp0s10 inet static | ||
| + | address 10.2XX.1.1/24 | ||
| + | </pre> | ||
| + | |||
| + | =Hosts= | ||
| + | *cat /etc/hosts | ||
| + | <pre> | ||
| + | 127.0.0.1 localhost | ||
| + | 127.0.1.1 fw.it2XX.int fw | ||
| + | |||
| + | # The following lines are desirable for IPv6 capable hosts | ||
| + | ::1 localhost ip6-localhost ip6-loopback | ||
| + | ff02::1 ip6-allnodes | ||
| + | ff02::2 ip6-allrouters | ||
| + | </pre> | ||
| + | =Resolver= | ||
| + | *cat /etc/resolv.conf | ||
| + | search it2XX.int | ||
| + | nameserver 192.168.Y.88 | ||
| + | =NAT mit nftables= | ||
| + | ;Datei erstellen, alles was drin ist kann raus | ||
| + | *cat /etc/nftables.conf | ||
| + | <pre> | ||
| + | #!/usr/sbin/nft -f | ||
| + | |||
| + | # Variablen | ||
| + | define LAN = 172.16.2XX.0/24 | ||
| + | define SERVERS = 10.2XX.1.0/24 | ||
| + | define DMZ = 10.88.2XX.0/24 | ||
| + | |||
| + | # Alte Regeln löschen (flush) | ||
| + | flush table ip nat | ||
| + | |||
| + | # NAT-Tabelle erstellen/verwenden | ||
| + | table ip nat { | ||
| + | chain postrouting { | ||
| + | type nat hook postrouting priority 100; policy accept; | ||
| + | |||
| + | # DMZ nach 192.168.Y.0/24 - kein NAT (RETURN) | ||
| + | ip saddr $DMZ ip daddr 192.168.Y.0/24 return | ||
| + | |||
| + | # DMZ nach 10.88.0.0/16 - kein NAT (RETURN) | ||
| + | ip saddr $DMZ ip daddr 10.88.0.0/16 return | ||
| + | |||
| + | # DMZ nach außen (enp0s3) - Masquerade | ||
| + | ip saddr $DMZ oif enp0s3 masquerade | ||
| + | |||
| + | # LAN nach außen - Masquerade | ||
| + | ip saddr $LAN oif enp0s3 masquerade | ||
| + | |||
| + | # SERVERS nach außen - Masquerade | ||
| + | ip saddr $SERVERS oif enp0s3 masquerade | ||
| + | } | ||
| + | } | ||
| + | </pre> | ||
| + | ;Firewall aktivieren | ||
| + | *systemctl enable nftables --now | ||
| + | |||
| + | =Forward= | ||
| + | *echo "net.ipv4.ip_forward=1" > /etc/sysctl.d/99-ipforward.conf | ||
| + | *sysctl -p /etc/sysctl.d/99-ipforward.conf | ||
| + | |||
| + | =Reboot= | ||
| + | *systemctl reboot | ||
| + | |||
| + | |||
| + | |||
| + | |||
= Firewall = | = Firewall = | ||
{{#drawio:5102-firewall-01}} | {{#drawio:5102-firewall-01}} | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
= Fernzugriff per [[:Kategorie:SSH|SSH]] = | = Fernzugriff per [[:Kategorie:SSH|SSH]] = | ||
Version vom 27. März 2026, 15:05 Uhr
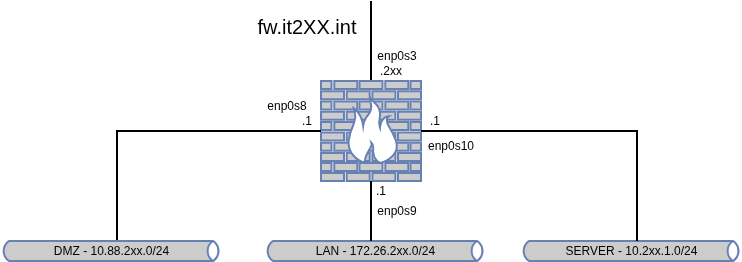
Wir klonen das debian-template
Folgendes stellen wir ein
- Name fw
- 4 GB RAM
- 4 CPUs
- 1. NIC WAN
- 2. NIC LAN
- 3. NIC LAN
- 4. NIC SERVERS
Erklärung
- XX = Platznummer
- Y = Klassensaal
Hostname
- hostnamectl set-hostname fw.it2XX.int
Interfaces
- cat /etc/network/interfaces
source /etc/network/interfaces.d/* # The loopback network interface auto lo iface lo inet loopback # The primary network interface #WAN auto enp0s3 iface enp0s3 inet static address 192.168.Y.2XX/24 gateway 192.168.Y.254 post-up ip route add 10.88.0.0/16 via 192.168.Y.88 #LAN auto enp0s8 iface enp0s8 inet static address 172.16.2XX.1/24 #DMZ auto enp0s9 iface enp0s9 inet static address 10.88.2XX.1/24 #SERVERS auto enp0s10 iface enp0s10 inet static address 10.2XX.1.1/24
Hosts
- cat /etc/hosts
127.0.0.1 localhost 127.0.1.1 fw.it2XX.int fw # The following lines are desirable for IPv6 capable hosts ::1 localhost ip6-localhost ip6-loopback ff02::1 ip6-allnodes ff02::2 ip6-allrouters
Resolver
- cat /etc/resolv.conf
search it2XX.int nameserver 192.168.Y.88
NAT mit nftables
- Datei erstellen, alles was drin ist kann raus
- cat /etc/nftables.conf
#!/usr/sbin/nft -f
# Variablen
define LAN = 172.16.2XX.0/24
define SERVERS = 10.2XX.1.0/24
define DMZ = 10.88.2XX.0/24
# Alte Regeln löschen (flush)
flush table ip nat
# NAT-Tabelle erstellen/verwenden
table ip nat {
chain postrouting {
type nat hook postrouting priority 100; policy accept;
# DMZ nach 192.168.Y.0/24 - kein NAT (RETURN)
ip saddr $DMZ ip daddr 192.168.Y.0/24 return
# DMZ nach 10.88.0.0/16 - kein NAT (RETURN)
ip saddr $DMZ ip daddr 10.88.0.0/16 return
# DMZ nach außen (enp0s3) - Masquerade
ip saddr $DMZ oif enp0s3 masquerade
# LAN nach außen - Masquerade
ip saddr $LAN oif enp0s3 masquerade
# SERVERS nach außen - Masquerade
ip saddr $SERVERS oif enp0s3 masquerade
}
}
- Firewall aktivieren
- systemctl enable nftables --now
Forward
- echo "net.ipv4.ip_forward=1" > /etc/sysctl.d/99-ipforward.conf
- sysctl -p /etc/sysctl.d/99-ipforward.conf
Reboot
- systemctl reboot
Firewall
Fernzugriff per SSH
- Jeder Host soll über das SSH-Protokoll administrierbar sein
- hinterlegen Sie den öffentlichen Schlüssel für die Nutzer kit und root auf der Firewall
- Der SSH-Server sollte nach Sicherstellung des Zugriffs über autorisierte SSH-Schlüssel keine Passwort-Authentifizierung mehr zulassen: SSH-Server Hardening
- Am Ende sollte jeder Host über ssh user@ip.oder.host.name erreichbar sein
Client Konfiguration
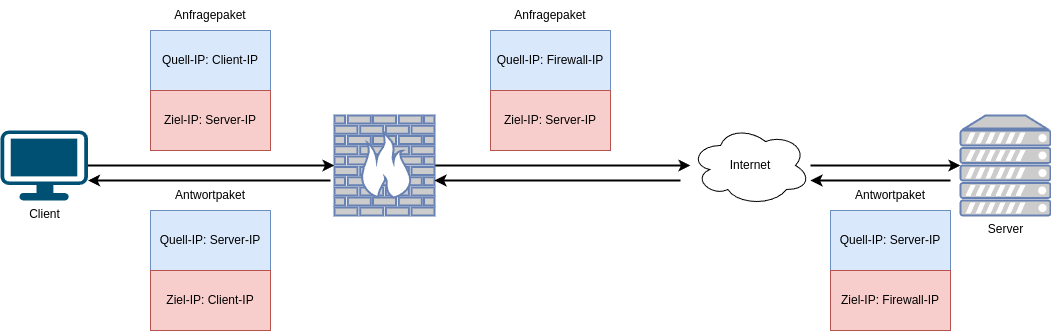
Routing und Masquerading
- Damit die Firewall als Internet-Router fungieren kann, muss die Quell-IP der Pakete umgeschrieben werden
- Dazu müssen Firewall-Regeln unter iptables oder nftables erstellt werden