Zentrale Benutzerverwaltung mit OpenLDAP und SSS: Unterschied zwischen den Versionen
Zur Navigation springen
Zur Suche springen
| Zeile 75: | Zeile 75: | ||
objectClass: organizationalUnit | objectClass: organizationalUnit | ||
ou: hosts | ou: hosts | ||
| + | |||
| + | dn: ou=sudo,dc=it213,dc=int | ||
| + | objectClass: organizationalUnit | ||
| + | ou: sudo | ||
== Anlegen == | == Anlegen == | ||
* ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f struktur.ldif | * ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f struktur.ldif | ||
| − | |||
| − | |||
| − | |||
= Ldapscripts = | = Ldapscripts = | ||
| Zeile 139: | Zeile 140: | ||
= nsswitch und pam anbinden via SSSD = | = nsswitch und pam anbinden via SSSD = | ||
| − | + | Anbindung für Debian 13 (Trixie). | |
== Installation == | == Installation == | ||
| Zeile 154: | Zeile 155: | ||
id_provider = ldap | id_provider = ldap | ||
auth_provider = ldap | auth_provider = ldap | ||
| + | |||
| + | # Erlaubt allen LDAP-Usern den Login | ||
| + | access_provider = permit | ||
| + | |||
sudo_provider = ldap | sudo_provider = ldap | ||
ldap_uri = ldap://ldap.it213.int | ldap_uri = ldap://ldap.it213.int | ||
ldap_search_base = dc=it213,dc=int | ldap_search_base = dc=it213,dc=int | ||
ldap_sudo_search_base = ou=sudo,dc=it213,dc=int | ldap_sudo_search_base = ou=sudo,dc=it213,dc=int | ||
| + | cache_credentials = True | ||
| + | |||
| + | # TLS Deaktivierung (WICHTIG für Testumgebungen ohne Zertifikate) | ||
ldap_id_use_start_tls = false | ldap_id_use_start_tls = false | ||
| − | + | ldap_auth_disable_tls_never_use_in_production = true | |
| − | ldap_tls_reqcert = | + | ldap_tls_reqcert = never |
</pre> | </pre> | ||
* chmod 600 /etc/sssd/sssd.conf | * chmod 600 /etc/sssd/sssd.conf | ||
* systemctl restart sssd | * systemctl restart sssd | ||
| − | == | + | == System-Integration == |
| − | + | * pam-auth-update --enable sss mkhomedir | |
| − | + | * sed -i 's/passwd:.*/passwd: files sss/' /etc/nsswitch.conf | |
| − | + | * sed -i 's/group:.*/group: files sss/' /etc/nsswitch.conf | |
| − | + | * sed -i 's/shadow:.*/shadow: files sss/' /etc/nsswitch.conf | |
| − | + | * echo "sudoers: files sss" >> /etc/nsswitch.conf | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | * pam-auth-update --enable mkhomedir | ||
| − | |||
| − | |||
| − | * | ||
| − | |||
| − | * | ||
| − | |||
| − | * | ||
| − | |||
| − | |||
| − | |||
| − | * | ||
| − | * | ||
| − | |||
| − | |||
| − | |||
| − | |||
= Sudo = | = Sudo = | ||
| − | == Sudo- | + | == Sudo-Regeln anlegen == |
| − | |||
* cat /root/sudo_rules.ldif | * cat /root/sudo_rules.ldif | ||
<pre> | <pre> | ||
| − | |||
| − | |||
| − | |||
| − | |||
dn: cn=%sudo,ou=sudo,dc=it213,dc=int | dn: cn=%sudo,ou=sudo,dc=it213,dc=int | ||
| + | objectClass: top | ||
objectClass: sudoRole | objectClass: sudoRole | ||
cn: %sudo | cn: %sudo | ||
| Zeile 229: | Zeile 200: | ||
* ldapaddusertogroup thomas sudo | * ldapaddusertogroup thomas sudo | ||
* ldapaddusertogroup tina sudo | * ldapaddusertogroup tina sudo | ||
| − | |||
| − | |||
| − | |||
| − | |||
== Testen == | == Testen == | ||
Version vom 2. April 2026, 07:16 Uhr
Installation
- passwort nach wahl festlegen
- apt update
- DEBIAN_FRONTEND=noninteractive apt install -y slapd ldap-utils
- slapd
- OpenLDAP Standalone Server
- ldap-utils
- Utilities zum Zugriff auf den LDAP Server
Grundkonfiguration
- dpkg-reconfigure slapd
Die folgende Tabelle führt die exakten englischen Abfragen auf, sowie die empfohlenen Eingaben für die it213.int Umgebung.
| Debconf Question | Description | Recommended Input / Choice |
|---|---|---|
| Omit OpenLDAP server configuration? | Determines if the installer should skip creating a database. | No |
| DNS domain name: | Used to construct the base DN of the LDAP directory. | it213.int |
| Organization name: | The name of the organization to use in the base DN. | it213 |
| Administrator password: | The password for the admin entry (cn=admin). | 123Start$ |
| Confirm password: | Re-enter the password for verification. | 123Start$ |
| Database backend to use: | The storage engine for the LDAP database. | MDB |
| Do you want the database to be removed when slapd is purged? | Whether to delete the data if the package is completely removed. | No |
| Move old database? | If a database already exists, should it be moved aside? | Yes |
| Allow LDAPv2 protocol? | Support for the obsolete LDAP version 2. | No |
OpenLDAP Manuelle Einrichtung (OLC)
OpenLDAP Manuelle Einrichtung (OLC)
Konfiguration des Clients
ldap.conf
- cat /etc/ldap/ldap.conf
base dc=it213, dc=int uri ldap://ldap.it213.int ldap_version 3 rootbinddn cn=admin, dc=it213, dc=int pam_password md5
Passwort für den Adminzugang eintragen
- echo 123Start$ > /etc/ldap.secret
Kontrolle
Stimmt der base dn
- ldapsearch -x -LLL
dn: dc=it213,dc=int objectClass: top objectClass: dcObject objectClass: organization o: it213 dc: it213
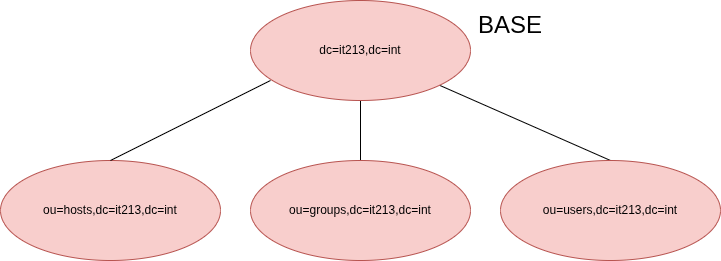
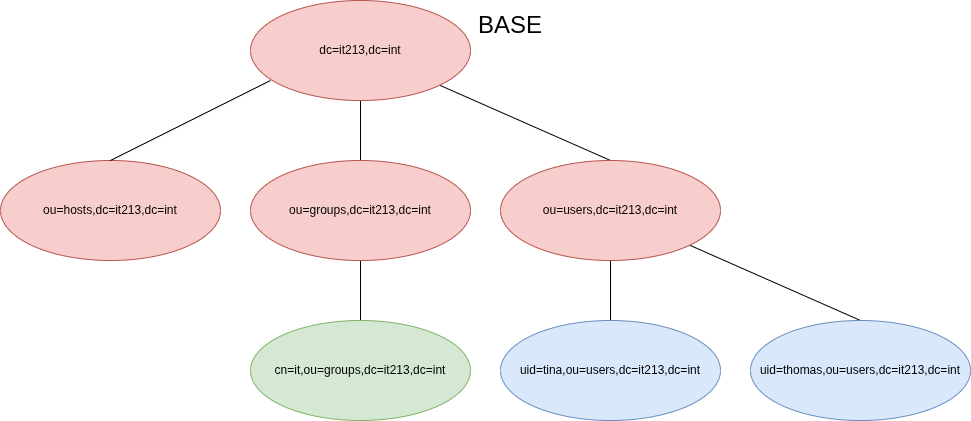
Grundstruktur
Erstellen
- cat /root/struktur.ldif
dn: ou=users,dc=it213,dc=int objectClass: organizationalUnit ou: users dn: ou=groups,dc=it213,dc=int objectClass: organizationalUnit ou: groups dn: ou=hosts,dc=it213,dc=int objectClass: organizationalUnit ou: hosts
dn: ou=sudo,dc=it213,dc=int objectClass: organizationalUnit ou: sudo
Anlegen
- ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f struktur.ldif
Ldapscripts
Installation
- apt install ldapscripts
Konfiguration
Hauptkonfiguration
- cat /etc/ldapscripts/ldapscripts.conf
SERVER="ldap://ldap.it213.int" SUFFIX="dc=it213,dc=int" GSUFFIX="ou=groups" USUFFIX="ou=users" MSUFFIX="ou=hosts" BINDDN="cn=admin,dc=it213,dc=int" USHELL="/bin/bash" UHOMES="/home/%u" CREATEHOMES="yes" HOMESKEL="/etc/skel" BINDPWDFILE="/etc/ldapscripts/ldapscripts.passwd" GIDSTART="10000" UIDSTART="10000" MIDSTART="20000" GCLASS="posixGroup" PASSWORDGEN="pwgen" RECORDPASSWORDS="no" PASSWORDFILE="/var/log/ldapscripts_passwd.log" LOGTOFILE="yes" LOGFILE="/var/log/ldapscripts.log" LOGTOSYSLOG="no" SYSLOGFACILITY="local4" SYSLOGLEVEL="info" LDAPSEARCHBIN="/usr/bin/ldapsearch" LDAPADDBIN="/usr/bin/ldapadd" LDAPDELETEBIN="/usr/bin/ldapdelete" LDAPMODIFYBIN="/usr/bin/ldapmodify" LDAPMODRDNBIN="/usr/bin/ldapmodrdn" LDAPPASSWDBIN="/usr/bin/ldappasswd" LDAPSEARCHOPTS="-o ldif-wrap=no"
Password Datei
- echo -n "123Start$" > /etc/ldapscripts/ldapscripts.passwd
Managment
Struktur
Gruppen anlegen
- ldapaddgroup it
Benutzer anlegen
- ldapadduser thomas it
- ldapadduser tina it
Passwörter setzen
- ldapsetpasswd thomas
- ldapsetpasswd tina
nsswitch und pam anbinden via SSSD
Anbindung für Debian 13 (Trixie).
Installation
- apt install sssd libnss-sss libpam-sss libsss-sudo
SSSD Konfiguration
- vim /etc/sssd/sssd.conf
[sssd] services = nss, pam, sudo domains = it213.int [domain/it213.int] id_provider = ldap auth_provider = ldap # Erlaubt allen LDAP-Usern den Login access_provider = permit sudo_provider = ldap ldap_uri = ldap://ldap.it213.int ldap_search_base = dc=it213,dc=int ldap_sudo_search_base = ou=sudo,dc=it213,dc=int cache_credentials = True # TLS Deaktivierung (WICHTIG für Testumgebungen ohne Zertifikate) ldap_id_use_start_tls = false ldap_auth_disable_tls_never_use_in_production = true ldap_tls_reqcert = never
- chmod 600 /etc/sssd/sssd.conf
- systemctl restart sssd
System-Integration
- pam-auth-update --enable sss mkhomedir
- sed -i 's/passwd:.*/passwd: files sss/' /etc/nsswitch.conf
- sed -i 's/group:.*/group: files sss/' /etc/nsswitch.conf
- sed -i 's/shadow:.*/shadow: files sss/' /etc/nsswitch.conf
- echo "sudoers: files sss" >> /etc/nsswitch.conf
Sudo
Sudo-Regeln anlegen
- cat /root/sudo_rules.ldif
dn: cn=%sudo,ou=sudo,dc=it213,dc=int objectClass: top objectClass: sudoRole cn: %sudo sudoUser: %sudo sudoHost: ALL sudoRunAsUser: ALL sudoRunAsGroup: ALL sudoCommand: ALL
- ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f /root/sudo_rules.ldif
Gruppenverwaltung
- ldapaddgroup sudo
- ldapaddusertogroup thomas sudo
- ldapaddusertogroup tina sudo
Testen
- su - thomas
- sudo -l
- sudo whoami