Iptables Failover
Version vom 16. Dezember 2022, 08:22 Uhr von Linkai.zhang (Diskussion | Beiträge)
Ziel
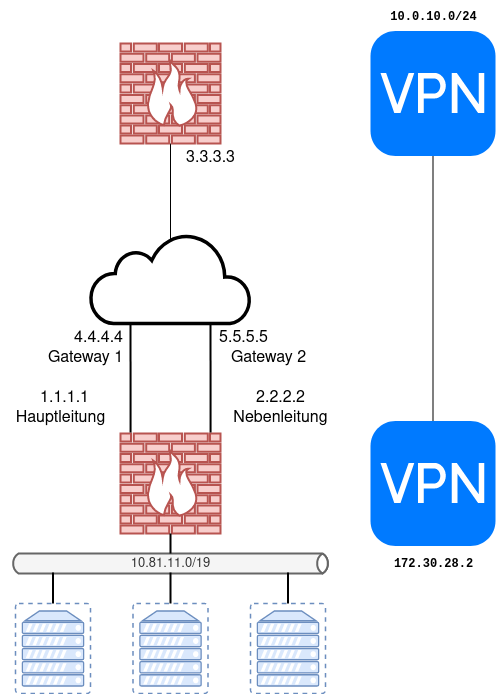
- Eine Firewall hat zwei Internetleitungen
- Eine Hauptleitung 1.1.1.1
- Eine Nebenleitung 2.2.2.2
- Falls die Hauptleitung ausfällt sollen alle Pakete (Pings, Webanfragen, VPNs) automatisch über die Nebenleitung laufen.
- VPN:
- IP: 3.3.3.3
- Lokales Netz: 10.0.10.0/24
Netzwerkkonfiguration
- This file describes the network interfaces available on your system
- and how to activate them. For more information, see interfaces(5).
source /etc/network/interfaces.d/*
- The loopback network interface
auto lo iface lo inet loopback
- The primary network interface
auto ens18 iface ens18 inet static
address 10.81.240.3/21 gateway 10.81.240.1
auto ens19 iface ens19 inet static
address 10.81.96.2/19 post-up ip rule add fwmark 200 table 200 post-up ip rule add from 10.81.96.2 table 200 pre-down ip rule del fwmark 200 table 200 pre-down ip rule del from 10.81.96.2 table 200 post-up ip route add default via 10.81.96.1 table 200
auto ens20
iface ens20 inet static
address 10.81.11.1/19 dns-nameservers 10.81.0.2
Firewall
Variablen
- vi /usr/local/etc/firewall.cfg
VODDEV=ens18 TELDEV=ens19 TELIP="10.81.96.2" VODIP="10.81.240.3" LANDEV=ens20 LAN="10.81.0.0/19" LANIP="10.81.11.1"
Regeln
- vi /usr/local/sbin/firewall
#!/bin/bash
#Einlesen der Konfigurationsdatei
source /usr/local/etc/firewall.cfg
echo normal > /tmp/fw.status
case $1 in
start)
echo "starte firewall"
#Löschen aller Reglen
iptables -F
iptables -F -t nat
iptables -F -t mangle
iptables -X
iptables -X -t nat
iptables -X -t mangle
#Setzen der Default Policy auf DROP
iptables -P INPUT DROP
iptables -P OUTPUT DROP
iptables -P FORWARD DROP
#Aktivieren des Connection Tracking Konzeptes
iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A FORWARD -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A OUTPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
#Verkehr von Rechner hinaus freischalten
iptables -A OUTPUT -m state --state NEW -j ACCEPT
#Verkehr über das loopback device freischalten
iptables -A INPUT -i lo -m state --state NEW -j ACCEPT
#Verkehr zum Rechner ZUM TCP PORT 22 erlauben
iptables -A INPUT -p tcp --dport 22 -m state --state NEW -j ACCEPT
#ICMP echo-request freigeschaltet
iptables -A INPUT -p icmp --icmp-type echo-request -m state --state NEW -j ACCEPT
iptables -A FORWARD -m state --state NEW -j ACCEPT
iptables -t mangle -N tel
iptables -t mangle -A tel -j MARK --set-mark 200
if test "$2" = "backup"
then
echo backup > /tmp/fw.status
iptables -A PREROUTING -t mangle -s $LAN ! -d $LAN -j tel
iptables -A OUTPUT -t mangle -s $LANIP ! -d $LAN -j tel
fi
iptables -t nat -A POSTROUTING -j SNAT -s $LAN -d 10.0.10.0/24 -o $TELDEV --to-source 172.30.28.2
iptables -t nat -A POSTROUTING -j SNAT -s $LAN -o $TELDEV --to-source $TELIP
iptables -t nat -A POSTROUTING -j SNAT -s $LAN -d 10.0.10.0/24 -o $VODDEV --to-source 172.30.28.1
iptables -t nat -A POSTROUTING -j SNAT -s $LAN -o $VODDEV --to-source $VODIP
iptables -A INPUT -j LOG --log-prefix "--iptables-drop-in--"
iptables -A OUTPUT -j LOG --log-prefix "--iptables-drop-out--"
iptables -A FORWARD -j LOG --log-prefix "--iptables-drop-for--"
;;
stop)
echo "stoppe firewall"
#Löschen aller Reglen
iptables -F
iptables -F -t nat
iptables -F -t mangle
iptables -X
iptables -X -t nat
iptables -X -t mangle
#Setzen der Default Policy auf ACCEPT
iptables -P INPUT ACCEPT
iptables -P OUTPUT ACCEPT
iptables -P FORWARD ACCEPT
;;
*)
echo "usage: $0 start|stop"
;;
esac