Zentrale Benutzerverwaltung mit OpenLDAP und SSS
Version vom 2. April 2026, 08:17 Uhr von Thomas.will (Diskussion | Beiträge)
Installation
- passwort nach wahl festlegen
- apt update
- DEBIAN_FRONTEND=noninteractive apt install -y slapd ldap-utils
- slapd
- OpenLDAP Standalone Server
- ldap-utils
- Utilities zum Zugriff auf den LDAP Server
Grundkonfiguration
- dpkg-reconfigure slapd
Die folgende Tabelle führt die exakten englischen Abfragen auf, sowie die empfohlenen Eingaben für die it213.int Umgebung.
| Debconf Question | Description | Recommended Input / Choice |
|---|---|---|
| Omit OpenLDAP server configuration? | Determines if the installer should skip creating a database. | No |
| DNS domain name: | Used to construct the base DN of the LDAP directory. | it213.int |
| Organization name: | The name of the organization to use in the base DN. | it213 |
| Administrator password: | The password for the admin entry (cn=admin). | 123Start$ |
| Confirm password: | Re-enter the password for verification. | 123Start$ |
| Database backend to use: | The storage engine for the LDAP database. | MDB |
| Do you want the database to be removed when slapd is purged? | Whether to delete the data if the package is completely removed. | No |
| Move old database? | If a database already exists, should it be moved aside? | Yes |
| Allow LDAPv2 protocol? | Support for the obsolete LDAP version 2. | No |
OpenLDAP Manuelle Einrichtung (OLC)
OpenLDAP Manuelle Einrichtung (OLC)
Sudo Schema (Minimal, OLC)
- cat <<EOF > /root/sudo-schema.ldif
dn: cn=sudo,cn=schema,cn=config objectClass: olcSchemaConfig cn: sudo olcAttributeTypes: ( 1.3.6.1.4.1.15953.9.1.1 NAME 'sudoUser' DESC 'User(s) who may run sudo' EQUALITY caseExactMatch SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 ) olcAttributeTypes: ( 1.3.6.1.4.1.15953.9.1.2 NAME 'sudoHost' DESC 'Host(s) who may run sudo' EQUALITY caseExactMatch SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 ) olcAttributeTypes: ( 1.3.6.1.4.1.15953.9.1.3 NAME 'sudoCommand' DESC 'Command(s) to be executed by sudo' EQUALITY caseExactMatch SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 ) olcAttributeTypes: ( 1.3.6.1.4.1.15953.9.1.4 NAME 'sudoRunAsUser' DESC 'User(s) impersonated by sudo' EQUALITY caseExactMatch SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 ) olcAttributeTypes: ( 1.3.6.1.4.1.15953.9.1.5 NAME 'sudoRunAsGroup' DESC 'Group(s) impersonated by sudo' EQUALITY caseExactMatch SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 ) olcObjectClasses: ( 1.3.6.1.4.1.15953.9.2.1 NAME 'sudoRole' DESC 'Sudoer Entries' SUP top STRUCTURAL MUST cn MAY ( sudoUser $ sudoHost $ sudoCommand $ sudoRunAsUser $ sudoRunAsGroup ) )
EOF
- ldapadd -Y EXTERNAL -H ldapi:/// -f /root/sudo-schema.ldif
Konfiguration des Clients
ldap.conf
- cat /etc/ldap/ldap.conf
BASE dc=it213,dc=int URI ldap://ldap.it213.int ldap_version 3 rootbinddn cn=admin,dc=it213,dc=int
Passwort für den Adminzugang eintragen
- echo 123Start$ > /etc/ldap.secret
- chmod 600 /etc/ldap.secret
Kontrolle
Stimmt der base dn
- ldapsearch -x -LLL
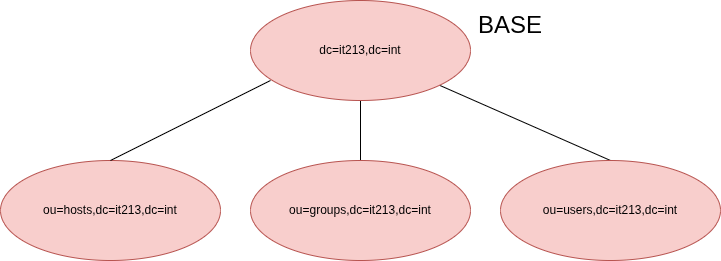
Grundstruktur
Erstellen
- cat /root/struktur.ldif
dn: ou=users,dc=it213,dc=int objectClass: organizationalUnit ou: users dn: ou=groups,dc=it213,dc=int objectClass: organizationalUnit ou: groups dn: ou=hosts,dc=it213,dc=int objectClass: organizationalUnit ou: hosts dn: ou=sudo,dc=it213,dc=int objectClass: organizationalUnit ou: sudo
Anlegen
- ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f /root/struktur.ldif
Ldapscripts
Installation
- apt install ldapscripts
Konfiguration
Hauptkonfiguration
- vim /etc/ldapscripts/ldapscripts.conf
SERVER="ldap://ldap.it213.int" SUFFIX="dc=it213,dc=int" GSUFFIX="ou=groups" USUFFIX="ou=users" MSUFFIX="ou=hosts" BINDDN="cn=admin,dc=it213,dc=int" USHELL="/bin/bash" UHOMES="/home/%u" CREATEHOMES="yes" HOMESKEL="/etc/skel" BINDPWDFILE="/etc/ldapscripts/ldapscripts.passwd" GIDSTART="10000" UIDSTART="10000" MIDSTART="20000"
Password Datei
- echo -n "123Start$" > /etc/ldapscripts/ldapscripts.passwd
- chmod 600 /etc/ldapscripts/ldapscripts.passwd
Managment
Gruppen anlegen
- ldapaddgroup it
Benutzer anlegen
- ldapadduser thomas it
- ldapadduser tina it
Passwörter setzen
- ldapsetpasswd thomas
- ldapsetpasswd tina
nsswitch und pam anbinden via SSSD
Installation
- apt install sssd libnss-sss libpam-sss libsss-sudo
SSSD Konfiguration
- vim /etc/sssd/sssd.conf
[sssd] services = nss, pam, sudo domains = it213.int [domain/it213.int] id_provider = ldap auth_provider = ldap access_provider = permit sudo_provider = ldap ldap_uri = ldap://ldap.it213.int ldap_search_base = dc=it213,dc=int ldap_sudo_search_base = ou=sudo,dc=it213,dc=int cache_credentials = True ldap_id_use_start_tls = false ldap_auth_disable_tls_never_use_in_production = true ldap_tls_reqcert = never
- chmod 600 /etc/sssd/sssd.conf
- systemctl restart sssd
System-Integration
- pam-auth-update --enable sss mkhomedir
Kontrolle
- cat /etc/nsswitch.conf
passwd: files systemd sss group: files systemd sss shadow: files systemd sss sudoers: files sss
Sudo
Sudo-Regeln anlegen
- cat /root/sudo_rules.ldif
dn: cn=%sudo,ou=sudo,dc=it213,dc=int objectClass: top objectClass: sudoRole cn: %sudo sudoUser: %sudo sudoHost: ALL sudoRunAsUser: ALL sudoRunAsGroup: ALL sudoCommand: ALL
- ldapadd -xD cn=admin,dc=it213,dc=int -w 123Start$ -f /root/sudo_rules.ldif
Gruppenverwaltung
- ldapaddgroup sudo
- ldapaddusertogroup thomas sudo
- ldapaddusertogroup tina sudo
Testen
- su - thomas
- sudo -l
- sudo whoami